Start a project
Powered by Snipcoins
- Welcome
- Features
- Advertisers
- Support
- Snipcoins
Discover
Businesses, projects and communities of individuals with similar interests in crypto.
Share
Snips of your latest trades, strategies and favorite projects or what's new with you.
Earn
Snipcoins (SNIPS) rewards for snipping and interacting. Withdraw your SNIPS rewards instantly.
Top features for you.
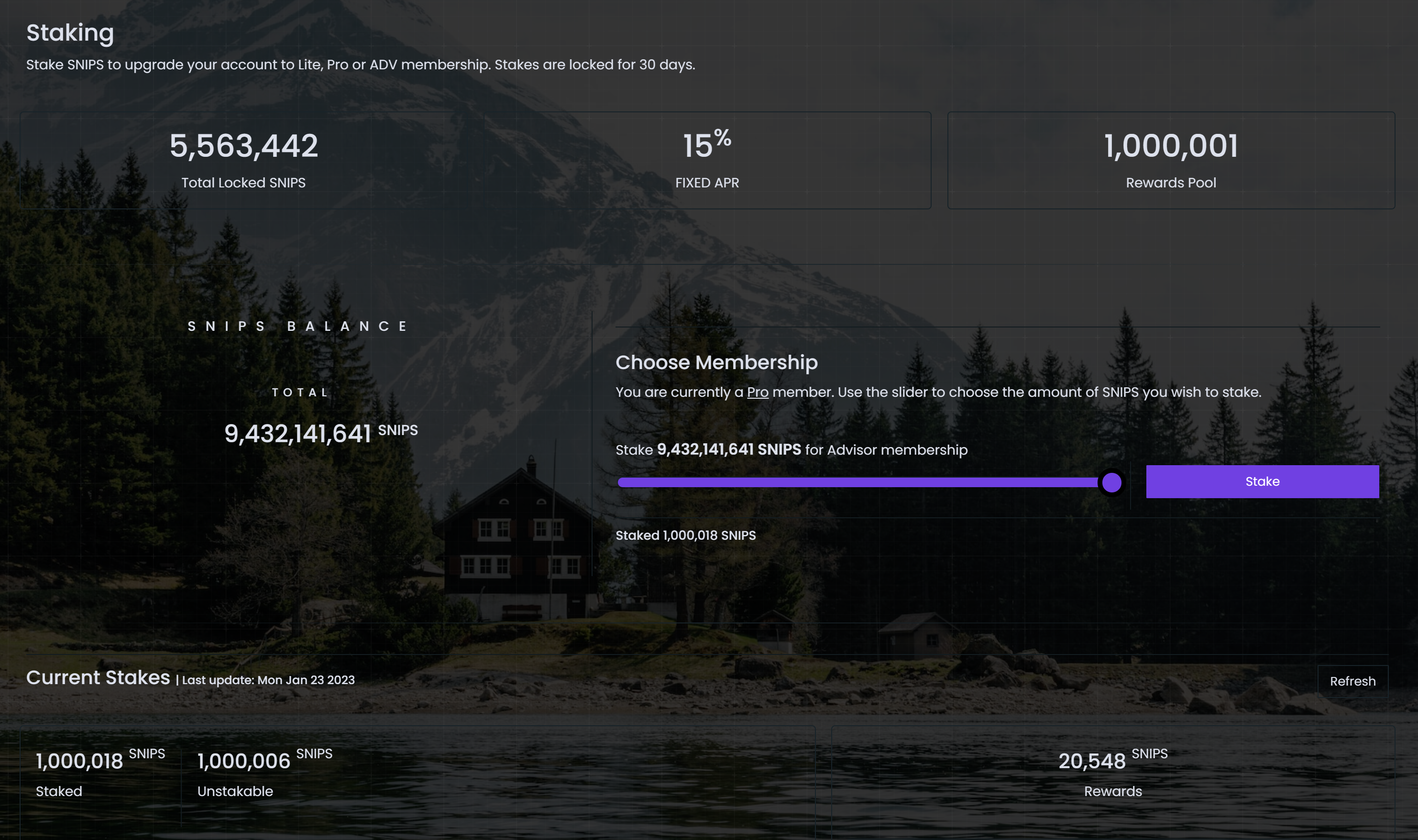
Staking.
Upgrade your Snipverse membership by staking Snipcoins. Unlock Lite, Pro or ADV membership level to start earning rewards for your contributions to the platform.
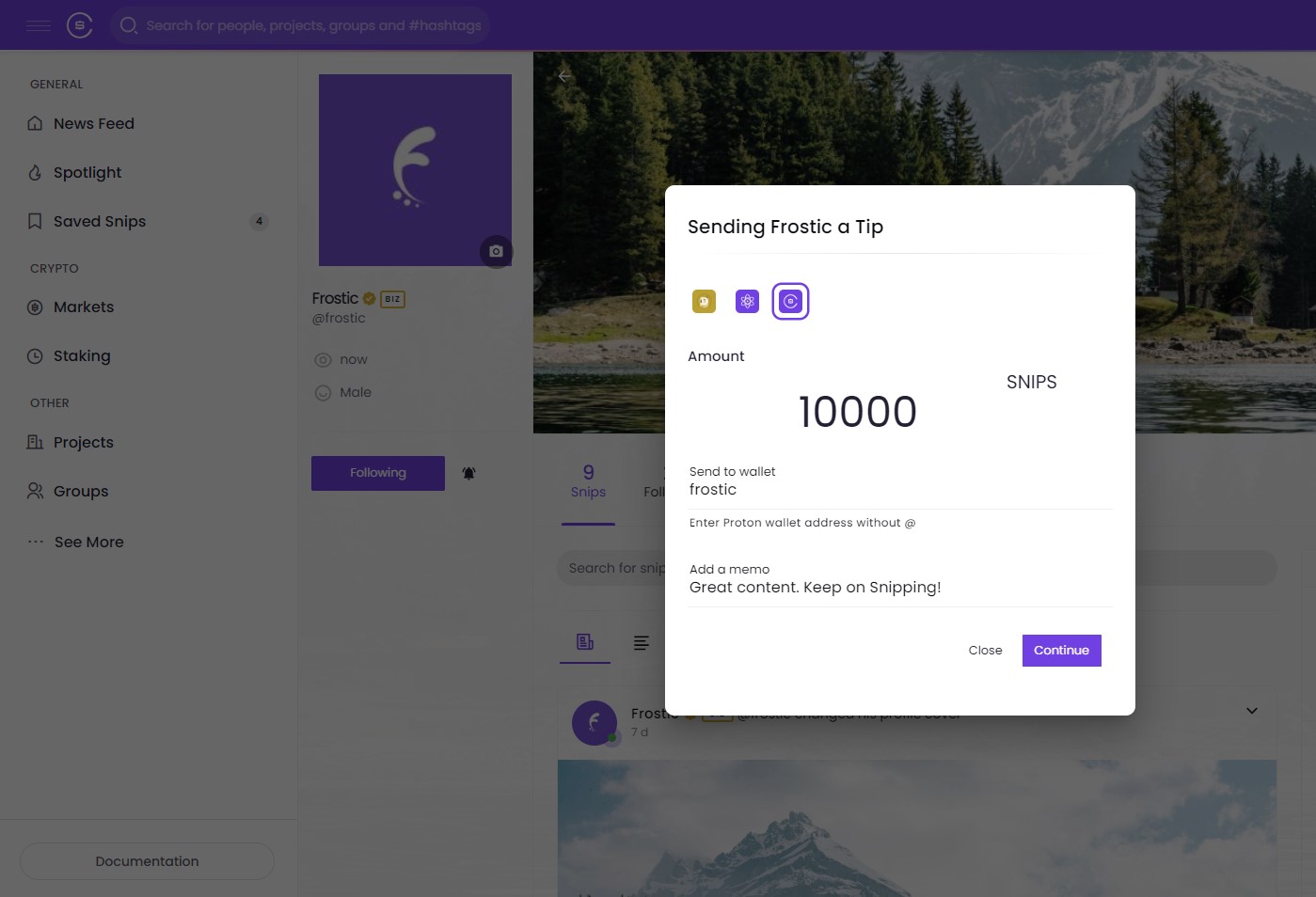
Tipping.
Show your appreciation for others' content by sending tips in the form of SNIPS, XPR, DOGE and other cryptocurrencies.
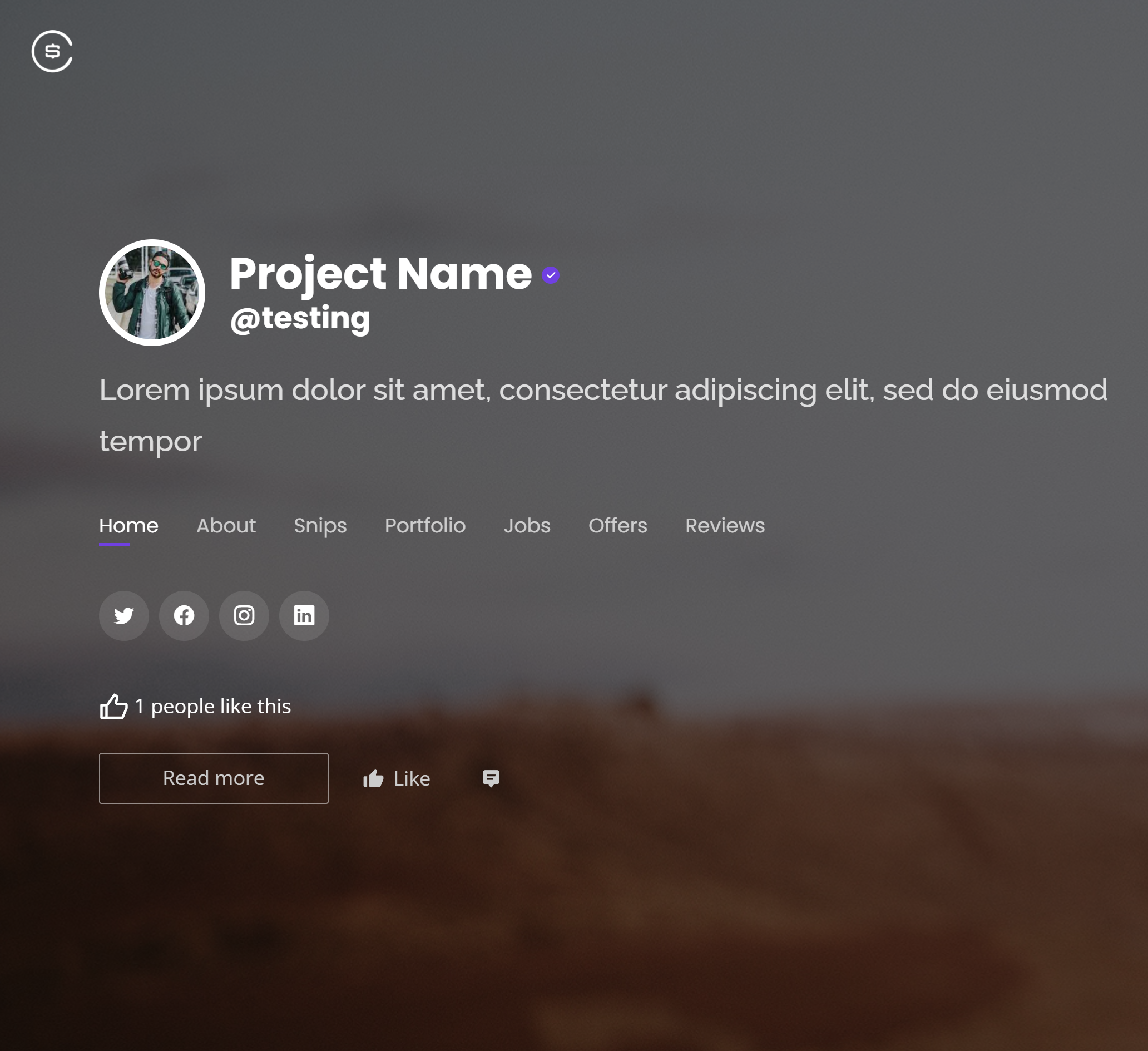
Projects.
Snipverse project page provides a platform for small businesses and projects in the crypto space to connect with their target audience and build their communities.
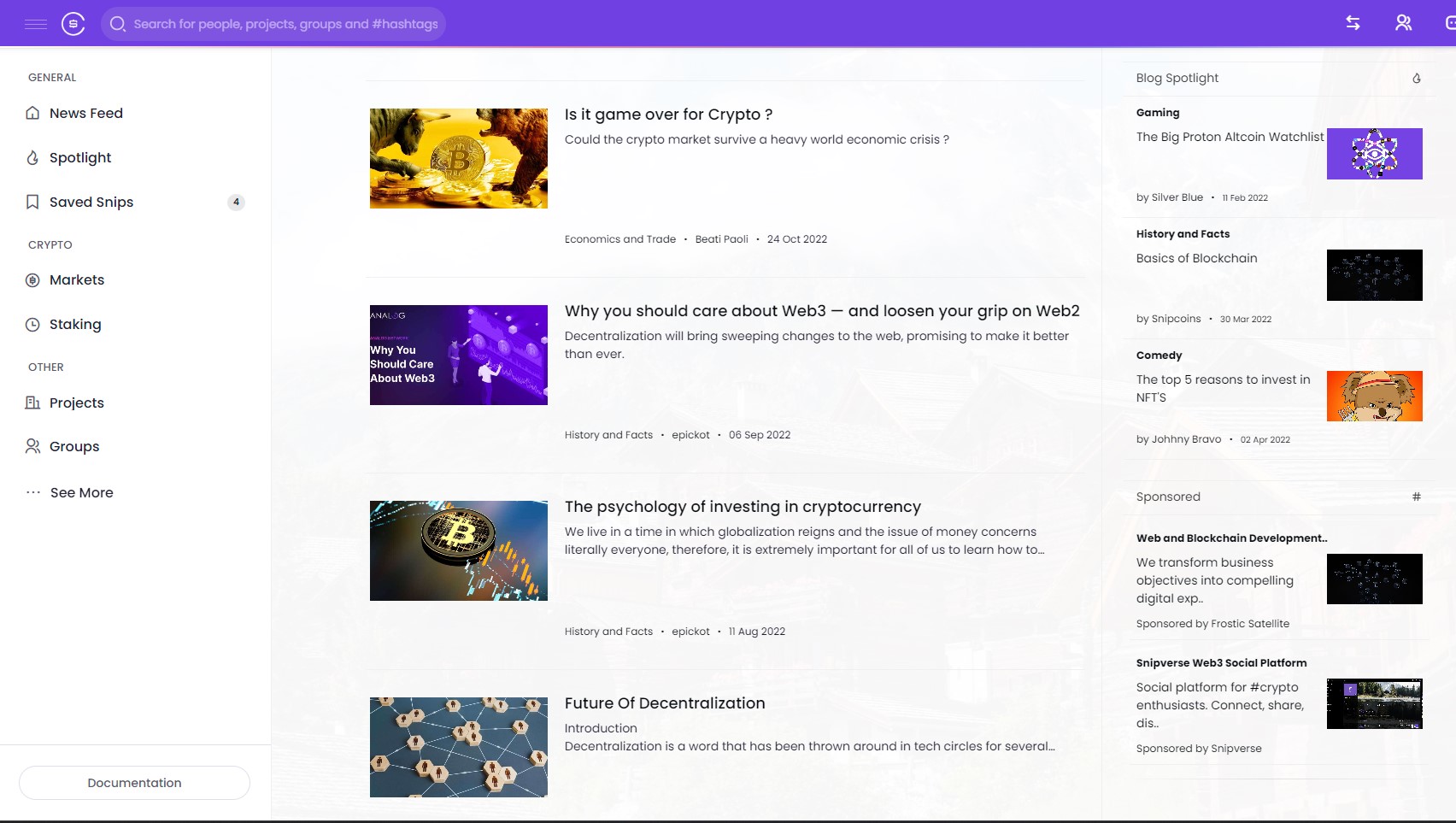
Blog.
Snipverse blog feature is an excellent way to make meaningful connections with others. Write engaging and informative posts and articles that grow your audience and foster a thriving community of like-minded people.
Advertising on Snipverse is a great opportunity for businesses and projects looking to reach a highly engaged and relevant audience of crypto enthusiasts and web3 professionals. With its growing user base, cost-effective pricing, and measurable results, Snipverse provides a unique and valuable opportunity for businesses and projects looking to grow and succeed in the web3 space.
Snipverse is a blockchain social media platform that provides a space for crypto enthusiasts, businesses and projects to connect, share, learn, and earn rewards. With its range of features and tools, Snipverse makes it easy for users to interact with others and build strong, engaged communities around their interests, businesses and projects.
Snipverse offers a staking membership program, where users can stake Snipcoins tokens to access exclusive features and benefits on the platform. By staking Snipcoins, users can upgrade their membership level and access additional features, such as increased rewards for content creation and interaction with other members.
No, Snipverse is integrated with Proton WebAuth.com wallet. WebAuth makes it easy, fast and secure for users to access their account and engage with others on the platform.
Snipverse provides a range of ways for users to earn rewards, including through content creation and interaction with other members. By contributing high-quality content and engaging with others on the platform, users can earn Snipcoins tokens, which can be used to access exclusive features and benefits on the platform.
The tipping system on Snipverse allows users to show their appreciation for others' content by sending tips in the form of SNIPS, XPR, DOGE, BTC and other cryptocurrencies. This provides a simple and easy way for users to reward others for their contributions to the community and encourage further engagement.
Yes, Snipverse provides instant withdrawal options for users to access their earnings from the platform. Whether you're looking to use your Snipcoins tokens to access exclusive features and benefits on the platform or simply to trade them for other assets, Snipverse makes it easy for you to access your rewards.
- Share
Share what's new and life moments with your friends.
- Discover
Discover new people, create new connections and make new friends.
- 100% Privacy
You have full control over your personal information that you share.
- More Security
Your account is fully secure. We never share your data with third party..